
Global cybersecurity company unmasks latest financial, opportunistic attacks in the region, shares tips on how to secure finances online
It is a common knowledge that the current health crisis, first detected in December of 2019, has drastically changed multiple aspects of human lives globally and in Asia Pacific (APAC). One of its most evident aftermaths is the significant uptick of digital payment adoption in the region.
Several reports have already put the numbers to prove this trend, but how about its tangible effects on the cybersecurity landscape of the financial sector?
After analysing the historical data from Kaspersky Security Network’s (KSN), Vitaly Kamluk, Director of Global Research & Analysis Team (GReAT) for APAC at Kaspersky, discovered that the increased cashless payments in APAC has paralleled the rise of banking Trojans in the region.
“Even before COVID-19, Asia Pacific has always been one of the leaders in digital payment adoption, driven by developed countries like China, Japan, South Korea and even India. This pandemic extended the use of this technology significantly further – particularly in still emerging economies in Southeast Asia and South Asia. As we all know, the lockdown restrictions forced everyone to shift their financial transactions online. But, now, after analysing the historical figures we have on financial threats, I also learned that there was another outbreak that started in early 2019 in APAC – banking Trojans,” says Kamluk.
Banking Trojans are one of the most dangerous species in the malware world. To put it simply, they are used to steal money from users’ bank accounts.
The goal of this malware is either to obtain access credentials or one-time passwords to online bank accounts or to manipulate the user and hijack control for the live online banking session from the legitimate owner.
Due to the uptick of online payment usage and the still-needing-improvement consumer attitudes towards protecting their devices, banking Trojan is among the most impactful malware for home users.
A decade long historical data analysis from KSN showed that South Korea was among the pioneer countries in APAC that suffered from banking Trojans throughout 2011-2012. However, since 2013 it showed significantly low relative numbers of infections and currently is at the bottom of the list of banking Trojans infected countries in the region.
Most of other developed countries show low statistics of banking Trojans detection too, while developing countries seem to have become and remain a hot spot for the criminals since 2019.
“Banking Trojans were not the biggest concern of many countries in APAC until 2019 when an outbreak of infections appeared in multiple countries at once. From then on there was no looking back. Our telemetry shows that this malicious threat has grown in terms of detections and reach. We see that it will continue to pose a significant threat to both financial organizations and individuals here as we continue to see more users and startups dipping their feet into the digital payments field,” adds Kamluk.
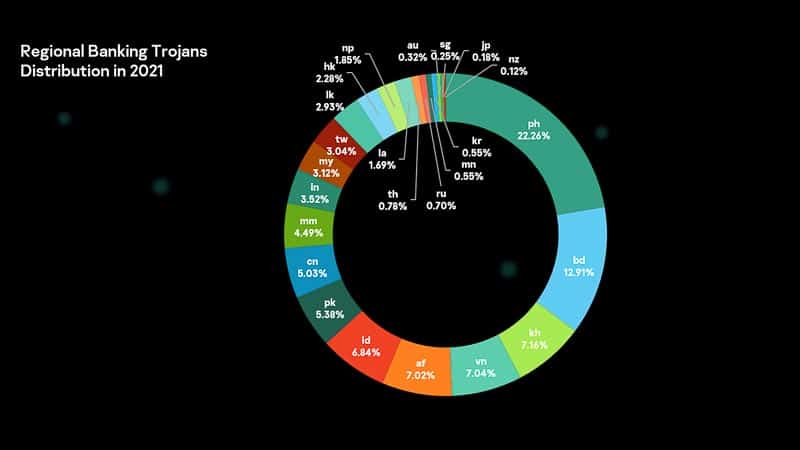
In terms of regional distribution, the Philippines logged the highest number of unique users attacked in APAC at 22.26% of all banking Trojans discovered in the region, followed by Bangladesh (12.91%), Cambodia (7.16%), Vietnam (7.04%), and Afghanistan (7.02%).
Kamluk also listed the types of financial threat actors, based on analysis of almost 300 publicly reported financial sector cyber-incidents since 2007. These include:
“The proportion of the unknown has grown over time, which is an alarming trend. With the growth of the number of attacks, there seems to be an alarming trend of financial institutions becoming less and less capable of identifying who attacked them. The unknown, unidentified threat actors were behind 60% of the attacks in 2020, but this number will likely grow up to 75% this year,” he says.
To better secure companies and individuals against these known and unknown cybercriminals, Kamluk shares the following reminders:
For financial organizations and enterprises, in general:
For individuals: